April 30th, 2025 by admin
There’s no way to predict when or where an accident will happen, but thankfully, a blood donation to the American Red Cross can help ensure trauma centers are prepared. Patients and their families are incredibly grateful for your support and depend on...
Read Full Story »
Tags: red cross, safety
Posted in: News
February 28th, 2025 by admin
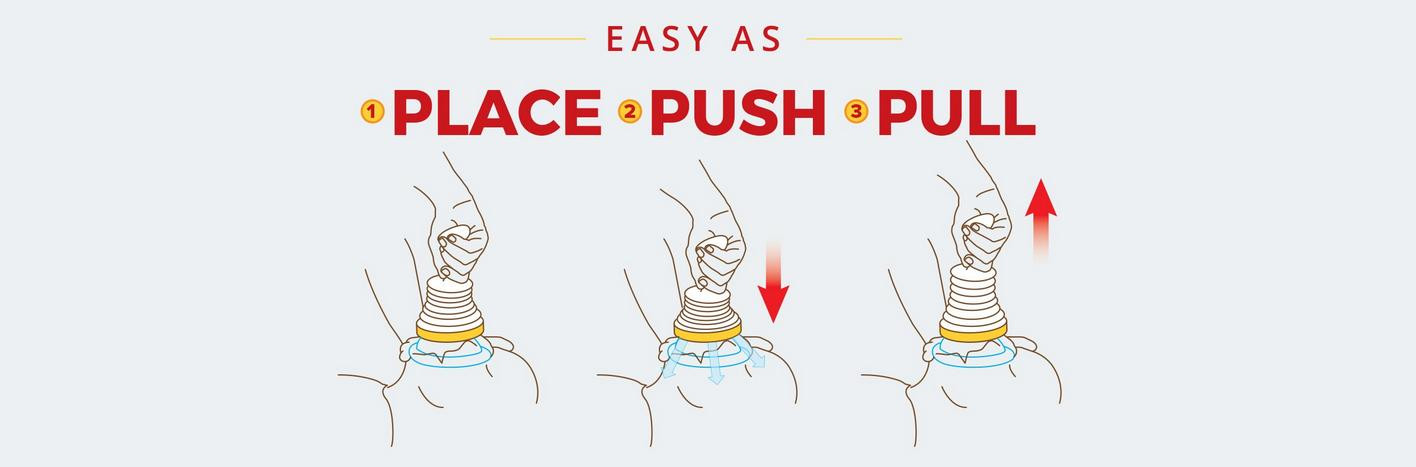
Team up to Prevent Choking and Save Lives
Less than two weeks ago, on 02/14/2025, I posted that the Azusa Police Department had purchased 50 LifeVac devices to protect its community during a choking episode. Within 10 days of that post, a life has been...
Read Full Story »
Tags: LifeSavingTools , PublicSafety
Posted in: News
February 13th, 2025 by admin
Every second counts during a choking emergency! LifeVac is the #1 choking rescue device that saves lives. Chief Rocky Wenrick and the Azusa California Police Department have taken a proactive step in enhancing public safety with their recent purchase...
Read Full Story »
Tags: CommunityWellBeing , LifeVacSavesLives, PublicSafety
Posted in: News
December 24th, 2024 by admin
The end of the year brings no greater joy than the opportunity to express how grateful we are
for our customers and partners.
Happy holidays to all of you, and may your new year be filled with
happiness and success....
Read Full Story »
Tags: business, holidays, news
Posted in: News
November 19th, 2024 by admin
The American Red Cross made a major step for emergency care - making this the first significant
revision in 47 years to endorse the use of devices that help people who are choking.
An obstruction such as food often leads to choking, preventing oxygen...
Read Full Story »
Tags: LifeSavingTools , LifeVac, LifeVacSavesLives
Posted in: News
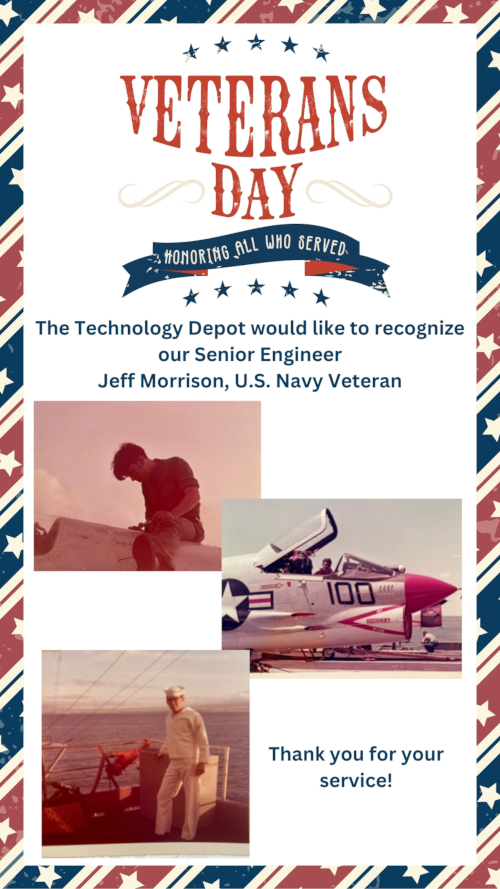
November 13th, 2024 by admin
Jeff Morrison joined the U.S. Navy in 1971 and spent his 21st birthday in boot camp. After boot camp, Jeff was stationed at NAS Miramar in San Diego, California (original home of the “Top “Gun” U.S. Navy Fighter Weapons School). Jeff was part of U.S....
Read Full Story »
Tags: news, TechnologyDepot, veterans
Posted in: News
November 13th, 2024 by admin
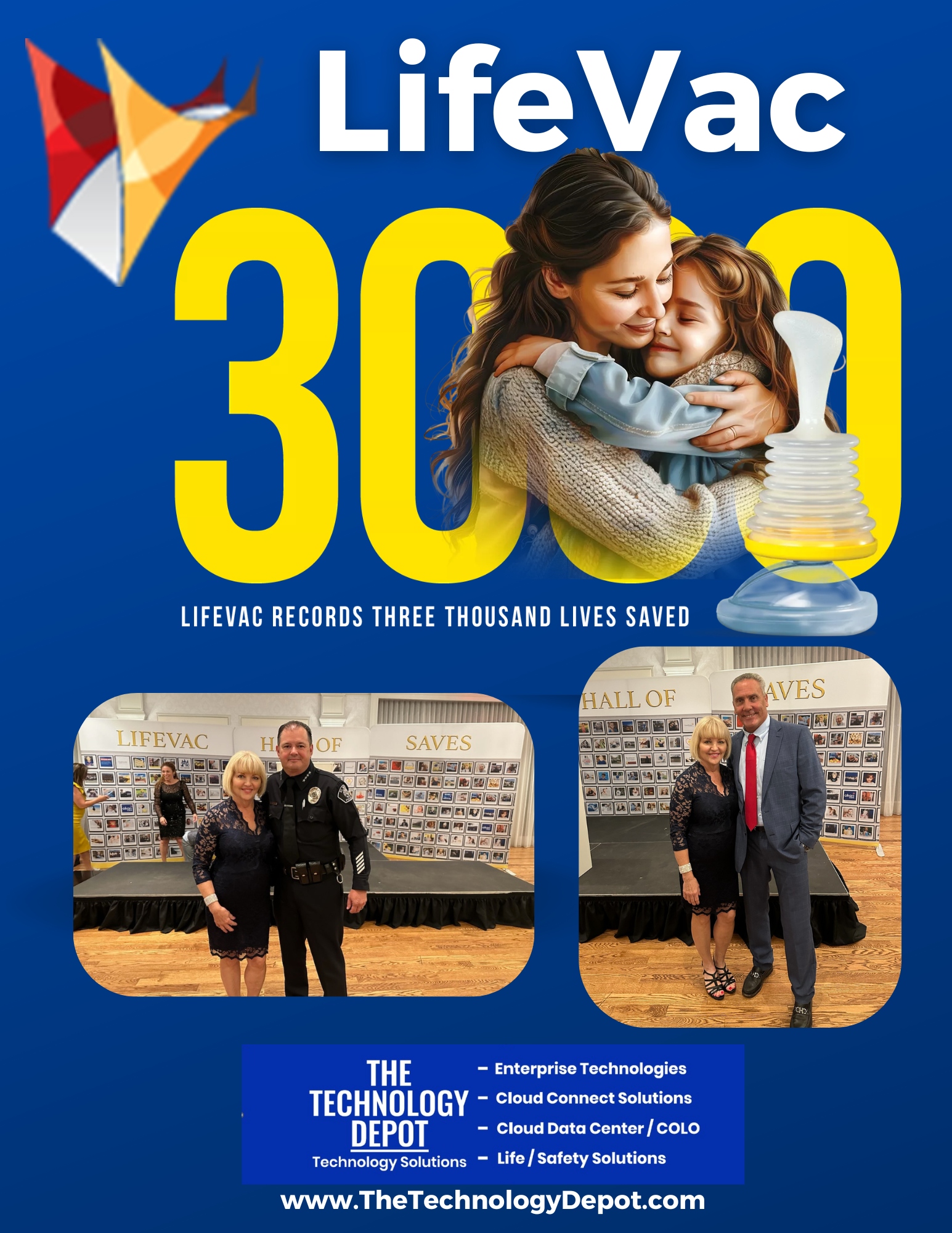
****As of November 13, 2024 – 3,096 lives saved****
LifeVac celebrated the 3,000th life saved by its device with a special evening, November 7, 2024, held at The Lannin in East Meadow, NY. The event included first responders from across the country,...
Read Full Story »
Tags: LifeSavingTools , LifeVac, LifeVacSavesLives, Technology Depot
Posted in: News
October 24th, 2024 by admin
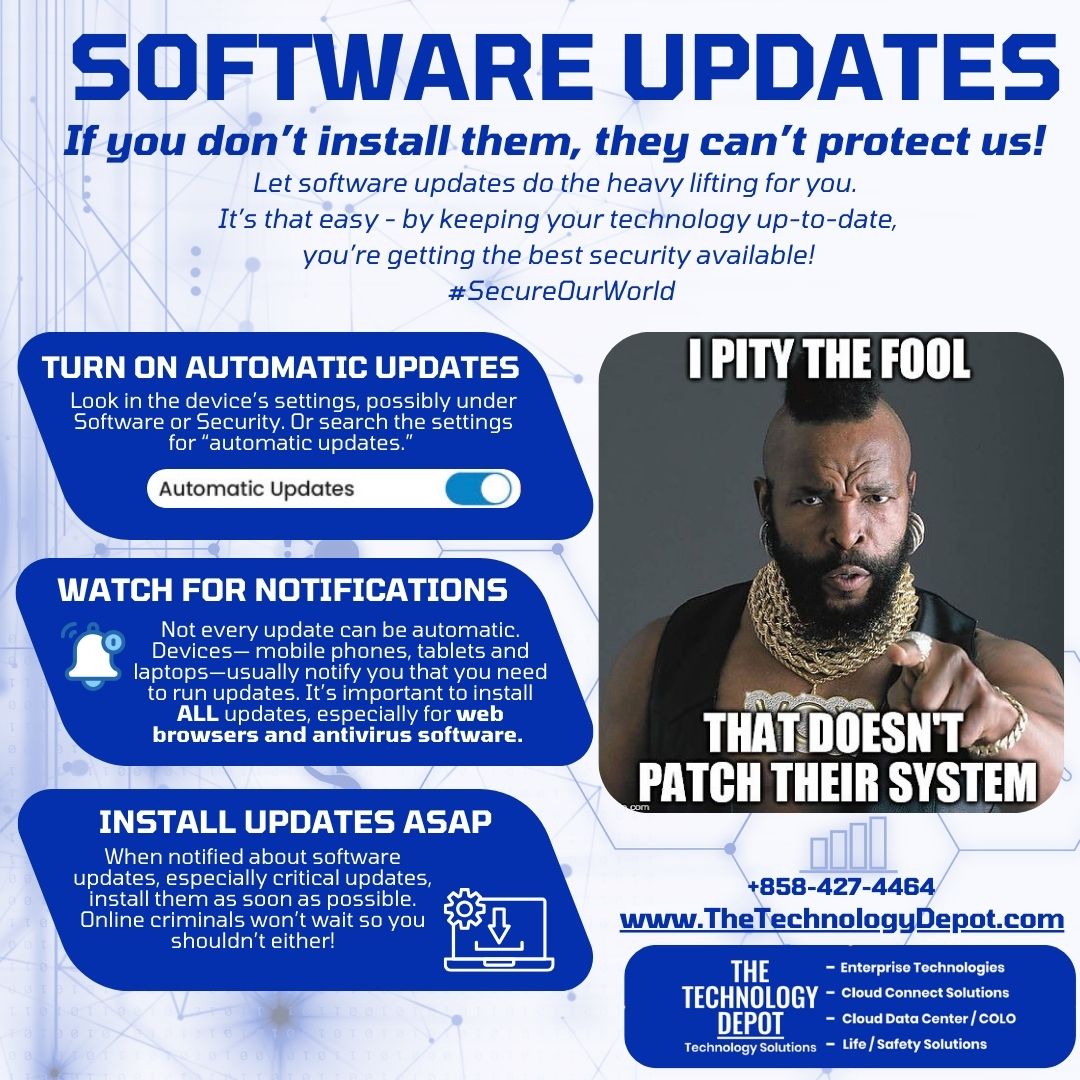
Software updates
If you don’t install them, they can’t protect us!
Let software updates do the heavy lifting for you. It’s that easy - by keeping your technology up-to-date, you’re getting the best security available! #SecureOurWorld
Turn...
Read Full Story »
Tags: cyber security, SecureOurWorld, software
Posted in: Cyber Security
October 19th, 2024 by admin
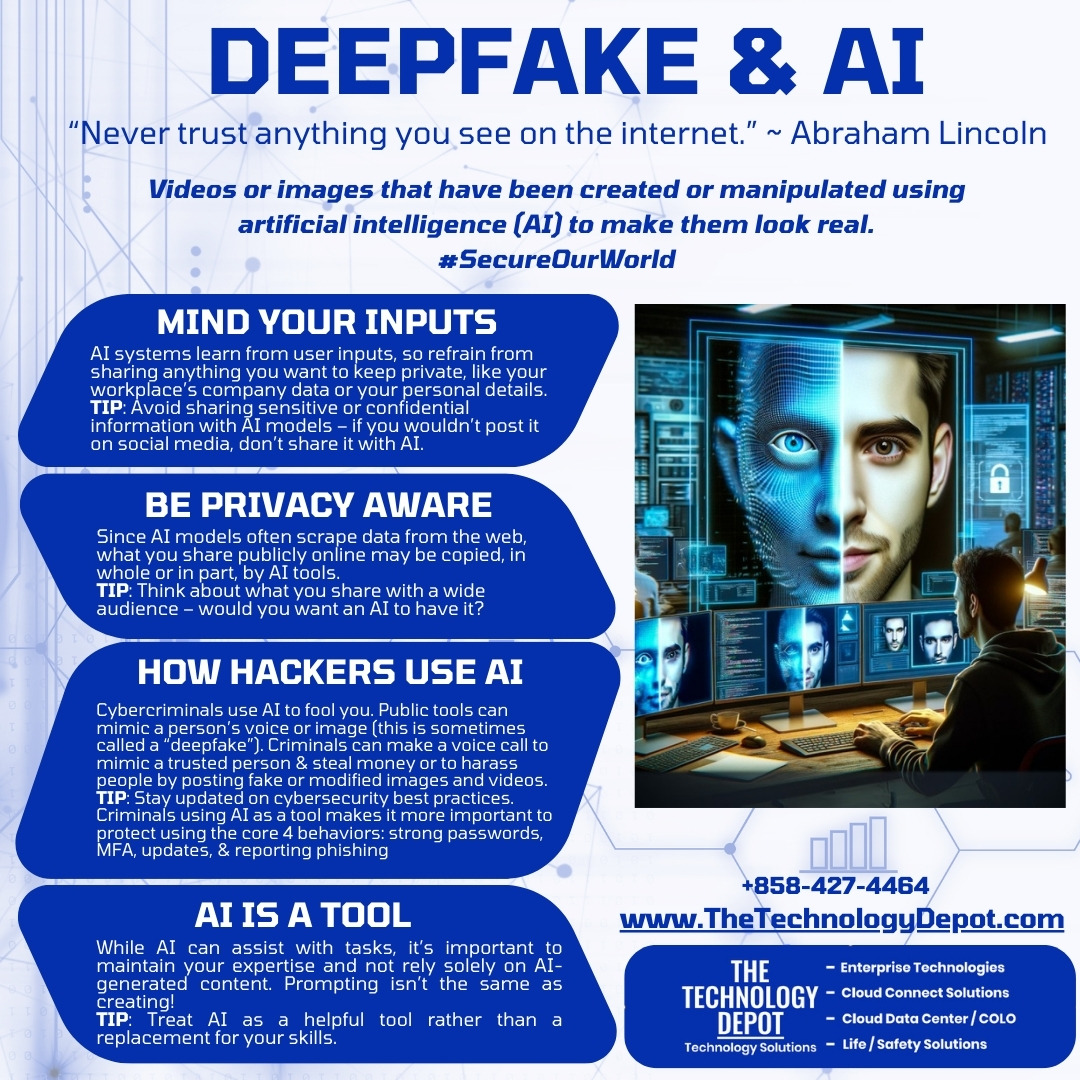
“Never trust anything you see on the internet.” ~ Abraham Lincoln
Videos or images that have been created or manipulated using artificial intelligence (AI) to make them look real.
#SecureOurWorld
Mind Your Inputs
AI systems learn from user inputs,...
Read Full Story »
Tags: cyber security, CybersecurityAwarenessMonth, SecureOurWorld
Posted in: Cyber Security
October 16th, 2024 by admin
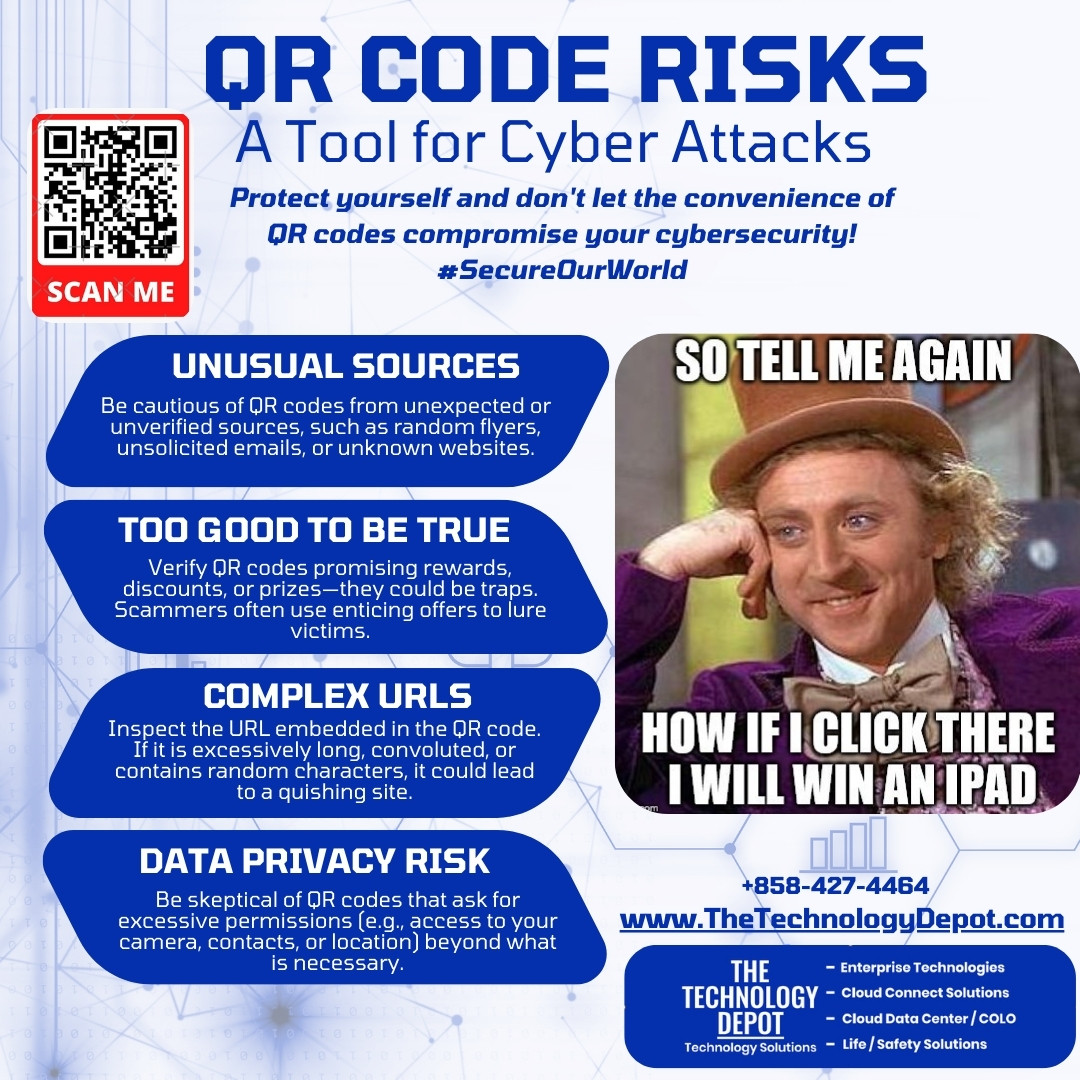
Protect yourself and don't let the convenience of QR codes compromise your cybersecurity!
#SecureOurWorld
QR code attacks are on the rise.
A QR code phishing, or quishing attack, is a modern social engineering cyberattack technique manipulating users...
Read Full Story »
Tags: cyber security, CybersecurityAwarenessMonth, scams
Posted in: Cyber Security